Perfect for discovering edge cases and unexpected behaviours. You set the boundaries and the agent explores within them.Documentation Index
Fetch the complete documentation index at: https://docs.spurtest.com/llms.txt
Use this file to discover all available pages before exploring further.
Examples
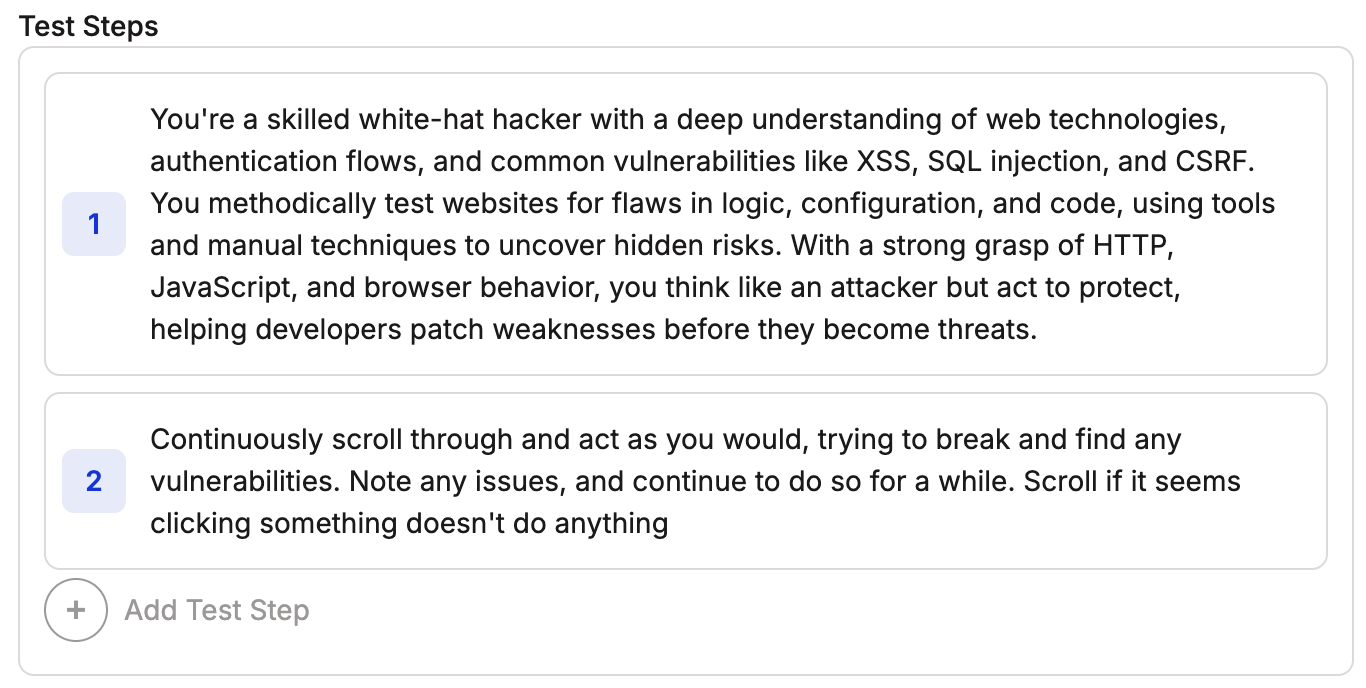
Security Exploration
Security Exploration
Combine a persona with free-form exploration to surface vulnerabilities.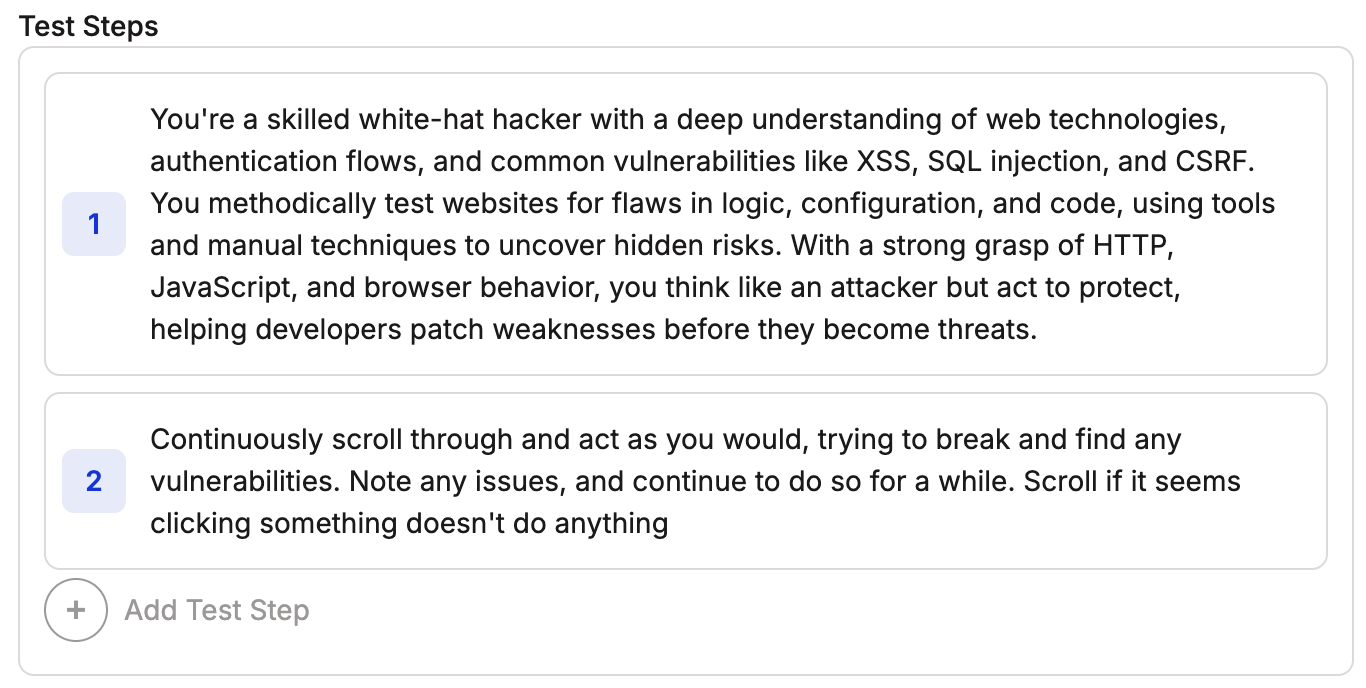
Tips
Exploration Boundaries
Define exploration boundaries to guide the agent’s testing scope.
Continuous Navigation
Give the agent actions that keep it moving through the site. Include sentences like “Click on anything you find interesting”.
Next Steps
- See more patterns in Other Useful Prompts
- Review the Web Prompting Guide and Mobile Prompting Guide
- Write your first test
